If you think AWS Direct Connect is just a private cable to AWS, that’s exactly where expensive architecture mistakes begin. In the real world, Direct Connect is not simply about speed. It’s about deciding when private connectivity actually solves a business problem, when it adds unnecessary complexity, and when a simpler option, like a VPN or even the Public Internet, is the smarter choice. That’s the difference between memorising AWS services and actually designing systems that work in production.
In this guide, you’ll learn the 7 essential concepts you need to understand AWS Direct Connect truly. By the end, you won’t just know what it is — you’ll know when to use it, when not to use it, and how to think like a cloud architect instead of just an exam candidate.
Table of Contents
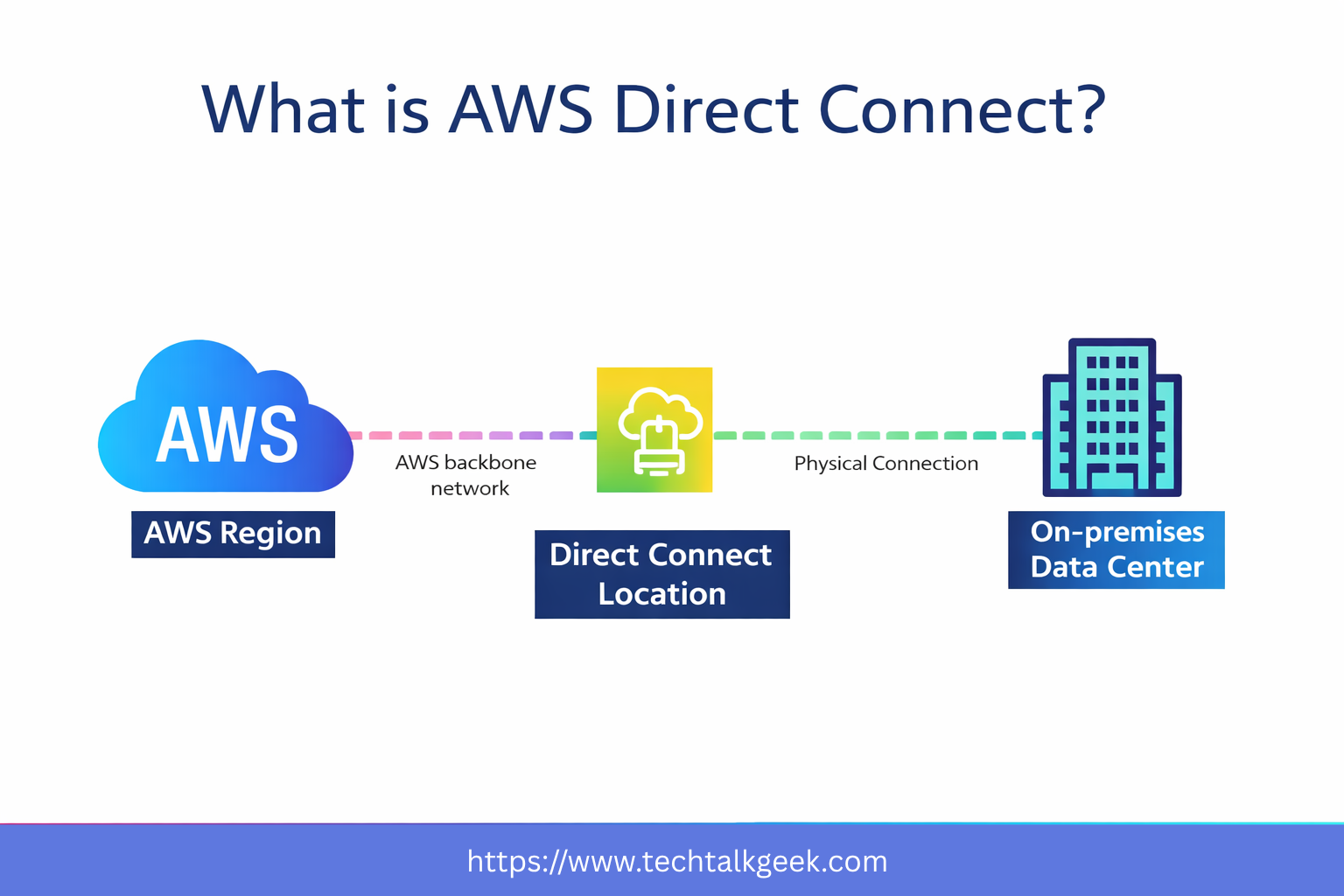
Concept 1: AWS Direct Connect Is About Dedicated Connectivity, Not Just Speed
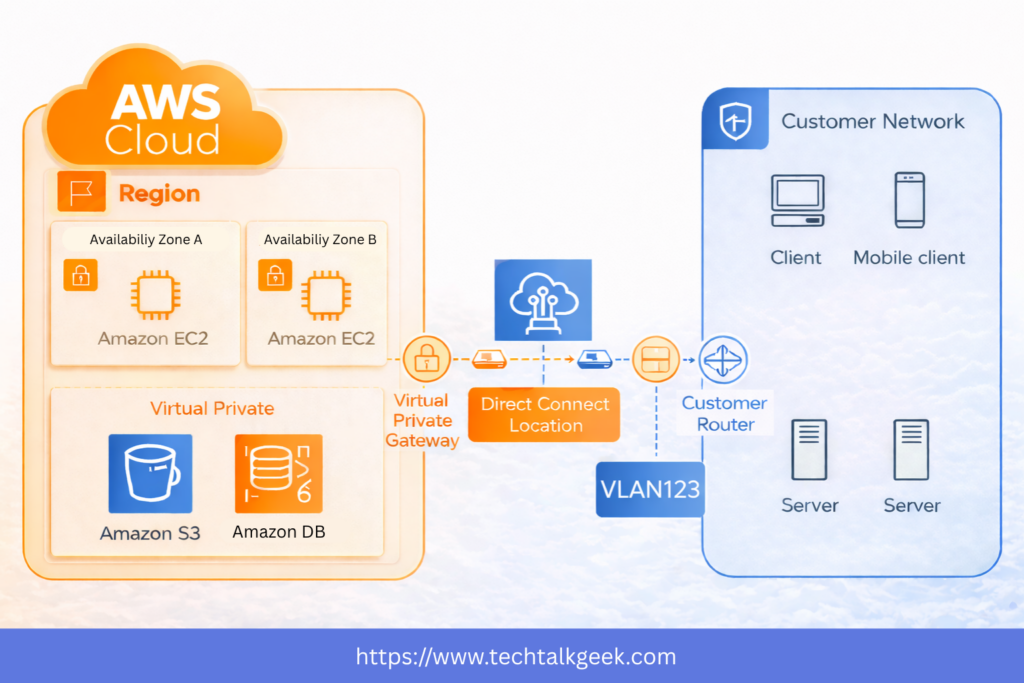
The first thing to understand is that AWS Direct Connect is a dedicated private network connection between your on-premises environment and AWS. If you want the official AWS definition and technical setup details, you can also refer to the AWS Direct Connect documentation. Instead of relying on the public Internet, your traffic travels through a more controlled and predictable path.
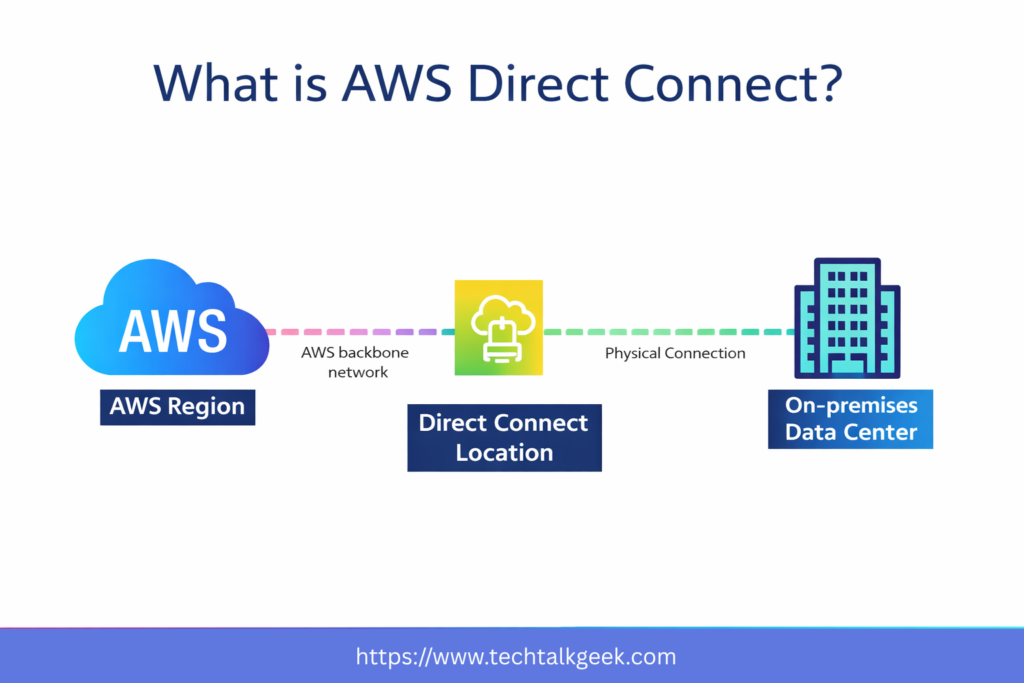
That sounds simple, but this is where many people misunderstand the service. Direct Connect is not just a “faster internet connection to AWS.” Its real value comes from consistency, stability, and controlled connectivity. Organisations use it because they want more reliable network behaviour for hybrid cloud workloads, not just raw bandwidth.
This matters most when businesses are running applications that depend on steady communication between on-premises systems and AWS resources. A company moving large data sets, syncing enterprise databases, or running hybrid applications may care much more about predictable throughput and lower variability than speed alone.
So if you want the simplest mental model, think of AWS Direct Connect as a premium dedicated lane between your network and AWS, designed for workloads where consistency matters.
Concept 2: Direct Connect Solves Hybrid Cloud Problems
AWS Direct Connect becomes relevant when organisations are running hybrid environments. That means part of the infrastructure still lives on-premises, while another part runs in AWS.
This is extremely common in the real world. A company may have legacy applications in a corporate data centre, internal databases hosted locally, and newer cloud workloads inside AWS. Once that happens, networking becomes a critical design problem. Those environments must communicate reliably, securely, and efficiently.
This is where Direct Connect is valuable. It provides organisations with a more stable way to connect their internal infrastructure to AWS. Instead of relying completely on internet-based paths, they can establish a dedicated connection for business-critical traffic.
That’s why Direct Connect is best understood as a hybrid architecture tool. It is not just an AWS networking feature. It is a way to support enterprise systems that span both on-premises infrastructure and the cloud.
Concept 3: Private VIF and Public VIF Serve Two Different Purposes
One of the most important concepts in AWS Direct Connect is understanding virtual interfaces, or VIFs.
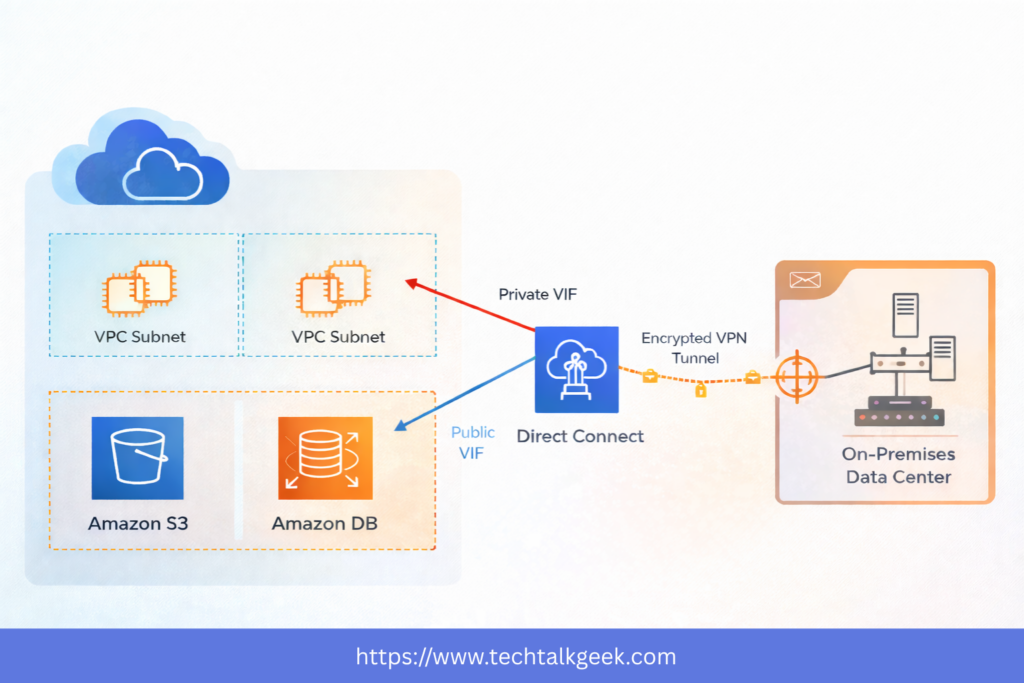
A VIF is essentially the logical path that determines what type of AWS traffic you want to send through the Direct Connect connection. This matters because not all AWS traffic is the same.
A Private VIF is used when your on-premises environment needs to access private resources inside your AWS VPC. This includes things like private EC2 instances, internal application servers, and private databases. If your goal is to connect your data centre to workloads within your VPC, this is the path to take.
A Public VIF is used when your on-premises environment needs to access AWS public services such as Amazon S3. This often surprises people because “public” makes it sound like traffic is flowing out onto the open Internet. But in this context, it means you are accessing AWS public endpoints through Direct Connect.
This distinction is incredibly important. If your company wants to reach private application infrastructure inside a VPC, that is one type of traffic. If it wants to back up files to S3 or interact with AWS public services, that is another. Direct Connect can support both, but only if you understand which VIF fits which use case.
Concept 4: Direct Connect Gateway Helps You Scale Beyond a Single VPC
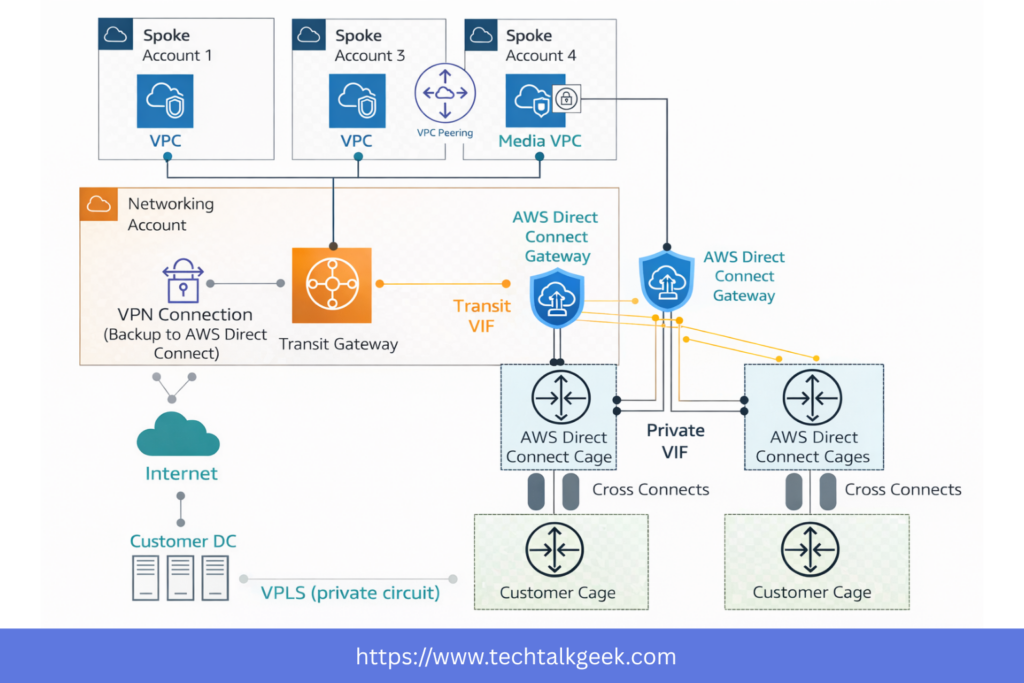
Things get more interesting when your AWS environment grows. Most organisations don’t keep a single VPC forever. They often expand across multiple VPCs, AWS accounts, and even regions.
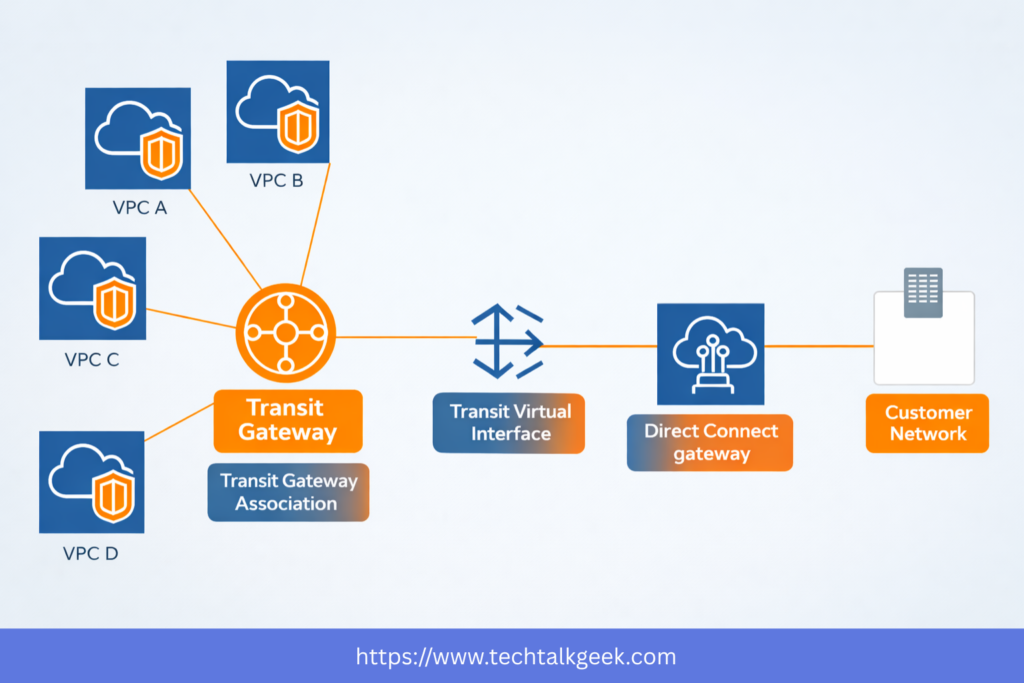
If you tried to connect your on-premises network to each VPC individually, your architecture would quickly become messy. This is where the Direct Connect Gateway becomes important. AWS also explains how AWS Direct Connect Gateway helps scale connectivity across multiple VPCs and Regions.
A Direct Connect Gateway allows you to extend your Direct Connect setup to multiple VPCs and multiple regions more cleanly. Instead of creating isolated, one-off designs, it provides a more scalable hybrid connectivity model.
This becomes especially valuable in larger AWS environments where networking needs to be centralised and manageable. In those scenarios, AWS Transit Gateway is often used together with Direct Connect to simplify routing across multiple VPCs. It helps organisations avoid duplicate connectivity patterns and provides a more elegant way to connect enterprise infrastructure to AWS at scale.
If you want the simple explanation, here it is: Direct Connect Gateway helps one Direct Connect setup reach more of your AWS environment without creating networking chaos.
Concept 5: VPN and Direct Connect Are Not Competitors — They Often Work Together
A common beginner mistake is treating Direct Connect vs. VPN as a simple either-or decision. In reality, many strong architectures use both together.
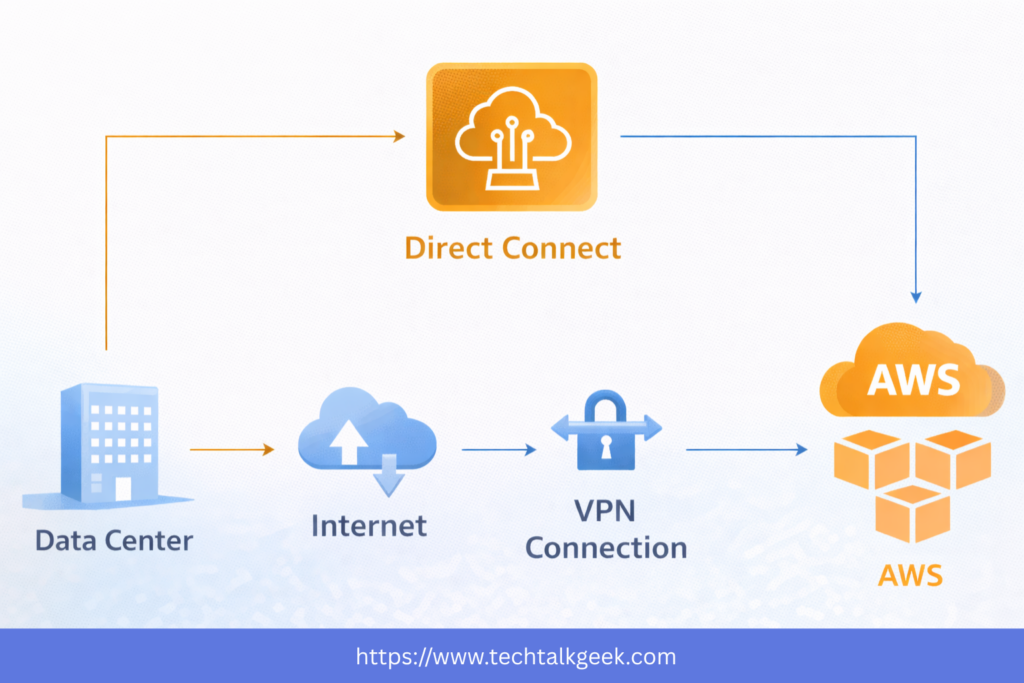
A Site-to-Site VPN is often faster to deploy and provides IPsec encryption over the Internet. If you’re new to hybrid connectivity, reviewing AWS Site-to-Site VPN alongside Direct Connect can make the differences much clearer. Direct Connect, on the other hand, gives you a private, dedicated path with more consistent performance. Each solves a different problem.
This is where many organisations get caught out: Direct Connect is not encrypted by default. It is private, but that does not automatically mean it is encrypted. That distinction matters a lot for compliance, security requirements, and real-world architecture.
That’s why many businesses run a VPN over Direct Connect. This gives them the best of both worlds: the stable, dedicated network path of Direct Connect, combined with VPN encryption.
So the smarter question is not always “Should I use Direct Connect or VPN?” Often, the better question is: Should I combine them based on my requirements?
That shift in thinking is what separates memorisation from architecture.
Concept 6: Direct Connect Is Powerful, But It Has Real Trade-Offs
One of the biggest mistakes people make is assuming Direct Connect is automatically the best option because it sounds more “enterprise.”
It isn’t.
AWS Direct Connect has real strengths, but it also comes with real trade-offs. It often involves physical provisioning, partner coordination, networking hardware, and setup lead times. In many cases, it can take weeks or even longer than a month to establish.
That means Direct Connect is usually a poor choice when a company needs a solution immediately. If the business needs hybrid connectivity this week and Direct Connect does not already exist, a VPN may be a more practical option.
It’s also important to remember that not every workload needs this level of networking sophistication. If your traffic is small, your connectivity needs are light, or your environment is still early in its cloud journey, Direct Connect may be unnecessary complexity.
Good architecture is not about choosing the most impressive service. It’s about choosing the service that actually fits the requirement.
That means Direct Connect is at its best when the problem is large enough, important enough, and long-term enough to justify the operational and architectural investment.
Concept 7: Resiliency Is Where Direct Connect Becomes Real Architecture
The final concept — and arguably the most important one — is resiliency.
Many beginner explanations make Direct Connect sound like a single connection you set up and forget. That is not how critical infrastructure should be designed.
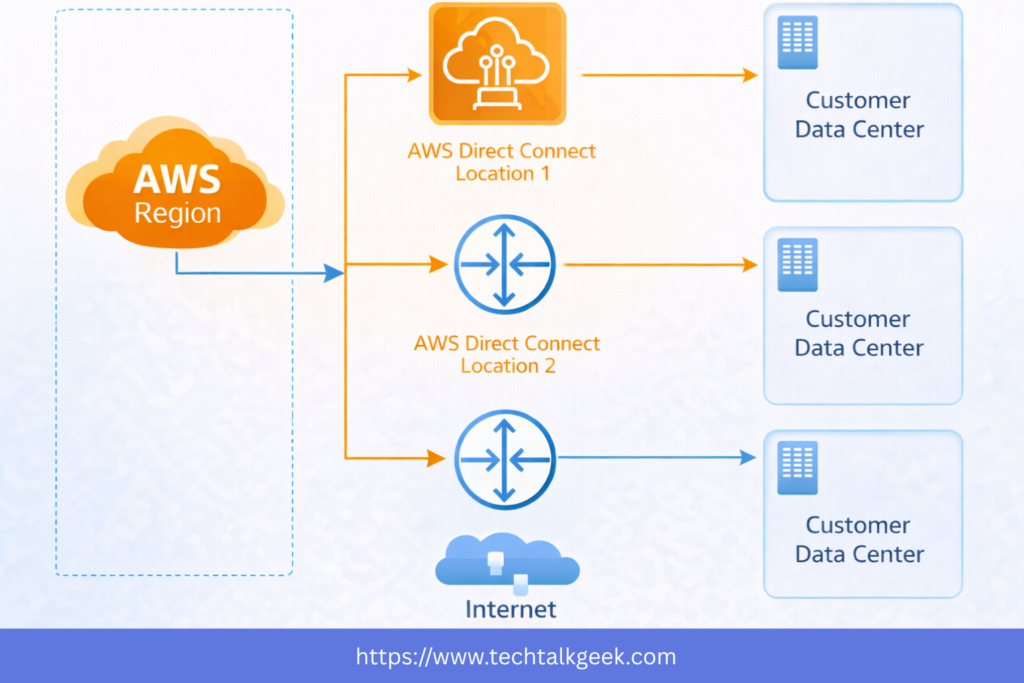
If your business depends on hybrid connectivity, then your network path itself becomes a critical dependency. And critical dependencies must be designed with failure in mind.
What happens if a circuit fails? What happens if a router fails? What happens if a Direct Connect location has an issue?
This is why resilient Direct Connect design often involves multiple connections across multiple locations. The goal is not just to “have a backup.” The goal is to reduce single points of failure and avoid a single issue taking down your hybrid architecture.
This is where AWS networking starts to become true architecture rather than just service memorisation. You stop asking, “Do I have Direct Connect?” and start asking, “Have I designed for failure?”
That’s a much more valuable question.
And in many production-grade environments, that’s also where VPN plays an important secondary role — as a failover or backup path in case your Direct Connect path becomes unavailable.
So if you want to think like an architect, don’t just learn Direct Connect as a service. Learn it as part of a resilient hybrid connectivity strategy.
When Should You Actually Use AWS Direct Connect?
Once you understand these seven concepts, the next question becomes much easier: when should you actually use AWS Direct Connect?
Direct Connect makes sense when your organisation needs consistent, private, high-value connectivity between on-premises infrastructure and AWS. It is especially useful for long-term hybrid workloads, high-throughput data transfer, enterprise integration, and environments where network predictability matters.
It is also highly relevant when you need to connect your business environment to multiple AWS VPCs and regions, especially as your architecture grows beyond a simple one-VPC design.
But Direct Connect is not always the right answer. If your organisation needs connectivity quickly, requires encryption immediately, or has only light networking demands, then a VPN may be the more practical option.
This is the real lesson: AWS Direct Connect is not impressive because it is private. It is impressive when it is justified.
Final Thoughts About AWS Direct Connect
The real skill is not knowing that AWS Direct Connect exists. The real skill is knowing when it creates value, when it creates unnecessary complexity, and when it hides a deeper design problem you should solve instead.
If you need private access to AWS VPC resources, think Private VIF. If you need access to AWS public services like S3, think Public VIF. If you need to scale across multiple VPCs and regions, think Direct Connect Gateway. If you need encryption or failover, think VPN alongside Direct Connect. And if you need resilience, think in terms of failure domains, not just extra cables.
That’s the mindset that turns AWS networking knowledge into real cloud architecture skills.
Leave a Reply